How to Compare Smart Fencing Hardware: A Definitive Editorial
The traditional concept of a fence—a static, passive boundary designed to provide a physical deterrent—is undergoing a fundamental shift. As property management, agricultural efficiency, and residential security converge with the Internet of Things (IoT), the “dumb” fence is being replaced by networked systems capable of sensing, reporting, and reacting. How to Compare Smart Fencing Hardware. This transition from passive wood and wire to active digital infrastructure requires a significant recalibration of how we perceive property boundaries. It is no longer enough to simply enclose a space; the modern requirement is to monitor that enclosure in real-time, often across vast distances or complex terrains.
Integrating technology into fencing is not merely about adding a camera or a motion sensor to a post. It involves a sophisticated layering of hardware, including conductive materials, low-power wide-area networks (LPWAN), and edge-computing processors. These systems are designed to distinguish between a harmless environmental interaction—such as a fallen branch or a heavy gust of wind—and a genuine breach attempt. This nuanced detection is the hallmark of high-tier smart fencing, separating professional-grade infrastructure from consumer-level gadgets that often suffer from “alert fatigue” due to frequent false positives.
For those tasked with securing high-value assets, managing large-scale livestock, or protecting sensitive residential perimeters, the decision-making process is fraught with technical trade-offs. The hardware must be resilient enough to survive decades of UV exposure, extreme temperature fluctuations, and physical impacts, while the internal electronics must remain precise and power-efficient. Consequently, the mandate to compare smart fencing hardware becomes an exercise in balancing structural integrity with digital reliability.
This article serves as a comprehensive technical and editorial deep dive into the current landscape of perimeter intelligence. It examines the hardware components that define the industry, the conceptual frameworks that govern their deployment, and the realistic failure modes that every system owner must anticipate. By moving beyond surface-level specifications, we aim to provide a definitive reference for those navigating the intersection of physical security and digital innovation.
Compare Smart Fencing Hardware
To effectively compare smart fencing hardware, one must first dismantle the oversimplification that “smart” simply means “connected.” In the context of perimeter security, hardware comparison is a multi-dimensional analysis of sensing modality, power autonomy, and communication latency. A common misunderstanding is that all smart fences rely on the same detection principles. In reality, the market is divided between systems that monitor the physical integrity of the wire (tension and conductivity) and those that use the fence as a mounting point for external sensors like LIDAR, vibration cables, or microwave barriers.
The risk of oversimplification often leads to a “one size fits all” procurement strategy, which inevitably fails during the implementation phase. For instance, a hardware suite designed for an equatorial agricultural setting—prioritizing solar efficiency and animal behavior patterns—will be fundamentally ill-suited for a high-security industrial site in a sub-arctic climate, where snow accumulation can dampen vibration sensors and battery chemistry might fail.
When we compare smart fencing hardware, we are looking at the convergence of three distinct subsystems:
-
The Physical Medium: The actual fence fabric (chain link, high-tensile wire, or mesh) which now acts as a carrier for sensors.
-
The Processor (The “Brain”): Local energizers or gateway controllers that interpret electrical pulses or data packets.
-
The Communication Backhaul: The method by which the hardware communicates with the user, whether through cellular (LTE/5G), Satellite, or LoRaWAN.
Understanding these layers is critical because a failure in one renders the others useless. A high-end vibration sensor is irrelevant if the communication hardware cannot penetrate the local topography or if the power supply is inconsistent.
Deep Contextual Background: From Barbed Wire to Pulse-Monitored Logic
The history of fencing is a history of property rights and resource management. The invention of barbed wire in the late 19th century revolutionized the American West, providing a cheap, effective way to manage cattle and define ownership. However, for over a century, the “technology” remained largely unchanged. The evolution toward “smart” systems began in the mid-20th century with the introduction of high-voltage, low-amperage electric fencing. While effective as a deterrent, these early systems were “blind”—they knew a pulse was sent, but they didn’t know if it was received or if the wire had been cut until a physical inspection occurred.
The systemic shift occurred with the integration of microprocessor-controlled energizers in the late 1990s and early 2000s. These devices could measure “return energy,” allowing the system to recognize a drop in voltage that indicated a leak or a break. The current era represents the third generation of this evolution: networked intelligence. We are no longer just measuring voltage; we are analyzing wave patterns, thermal signatures, and acoustic vibrations.
Today, the “systemic” nature of fencing means it is often integrated into broader security ecosystems. A smart fence is rarely a standalone product; it is a node in a network that might include drone deployment triggers, automated gate locks, and cloud-based logging. This evolution reflects a broader trend in infrastructure: the move from reactive maintenance (fixing it when it’s broken) to predictive analytics (identifying a weakening signal before a breach occurs).
Conceptual Frameworks and Mental Models
When evaluating how to compare smart fencing hardware, professional installers and security architects often use specific mental models to categorize the utility of various components.
1. The Detection-Delay-Response Triad
This is the foundational framework for all physical security. The hardware is assessed based on its ability to:
-
Detect: How quickly and accurately does the sensor identify an intrusion?
-
Delay: How long does the physical structure hold back the intruder after detection?
-
Response: Does the hardware provide enough data to allow for an effective human or automated response?
-
Limits: This model assumes a responsive force is available. If the fence is in a remote location with a four-hour response time, the “Delay” hardware becomes significantly more important than the “Detection” hardware.
2. The False Alarm Rate (FAR) vs. Probability of Detection (PoD)
There is an inverse relationship between sensitivity and reliability.
-
High PoD: Catches every movement but triggers on every bird or tumbleweed.
-
Low FAR: Only triggers on confirmed human/large animal breaches but might miss a sophisticated, slow-moving intruder.
-
Limits: No hardware achieves 100% in both. The goal is to find the “sweet spot” based on the specific environment.
3. The Energy Autonomy Model
In remote deployments, hardware is judged by its “Energy ROI.”
-
Active Systems: Require constant power (e.g., active infrared beams).
-
Passive Systems: Only consume significant power when a state change occurs (e.g., tension sensors).
-
Limits: Solar-based systems are limited by latitude and seasonal light cycles, which can create “dark windows” in security coverage.
Key Categories and Technical Trade-offs
Selecting the right hardware requires a granular understanding of the different technological “families” within the smart fencing world.
1. Strain-Gauge and Tension Sensors
These devices measure the physical tautness of the fence wires. If a wire is cut or climbed, the tension changes, triggering an alarm.
-
Pros: Highly reliable for anti-climb applications; very low power consumption.
-
Cons: Susceptible to false alarms in environments with extreme thermal expansion and contraction.
2. Acoustic Fiber Optic (AFO) Sensors
A fiber optic cable is threaded through or attached to the fence. The system sends light pulses through the cable and detects “micro-bends” caused by vibrations.
-
Pros: Can cover tens of kilometers with a single processor; immune to EMI (electromagnetic interference).
-
Cons: Expensive entry cost; requires specialized technicians for repairs/splicing.
3. Monitored Pulse Electric Hardware
This involves an energizer that sends a safe but sharp pulse of electricity. The “smart” aspect comes from the return-loop monitoring that alerts the user to grounding or wire-cutting.
-
Pros: Provides both a physical deterrent and a digital alert.
-
Cons: Often requires significant vegetation management to prevent grounding (weeds touching the wire).
4. Taut-Wire Electromechanical Systems
A hybrid of physical barriers and electrical switches. A disturbance moves a wire, which physically opens or closes a circuit.
-
Pros: Extremely low false alarm rate; proven in high-security military contexts.
-
Cons: High mechanical complexity; aesthetically industrial.
5. Microwave and Infrared Barriers
These are “virtual” fence components often used in conjunction with physical wire. They create an invisible plane of detection.
-
Pros: No physical contact required; works well in “clean” environments like warehouses.
-
Cons: Heavily affected by fog, heavy rain, or blowing snow.
6. IoT Integrated Gateways
The hardware that bridges the gap between the fence and the internet. Often uses LoRaWAN or NB-IoT.
-
Pros: Enables long-distance communication (up to 15km) without cellular subscriptions.
-
Cons: Requires line-of-sight or repeaters in mountainous terrain.
Core Hardware Modalities Comparison
| Feature | Tension Sensors | Fiber Optic (AFO) | Monitored Electric | Microwave Barriers |
| Primary Use | Anti-climb / Cut | Long-range Perimeter | Deterrence / Detection | Virtual Gates |
| Power Needs | Very Low | Moderate | High (Energizer) | Moderate |
| Maintenance | Mechanical Adjustments | Low (if protected) | High (Vegetation) | Low (Alignment) |
| Cost / Meter | Moderate | High | Low to Moderate | High |
| Sensitivity | Physical Displacement | Acoustic Vibration | Electrical Continuity | Line-of-Sight Break |
Real-World Deployment Scenarios and Constraints How to Compare Smart Fencing Hardware

The theoretical benefits of smart fencing often collide with the realities of the physical environment. To truly compare smart fencing hardware, we must look at how these systems behave under pressure.
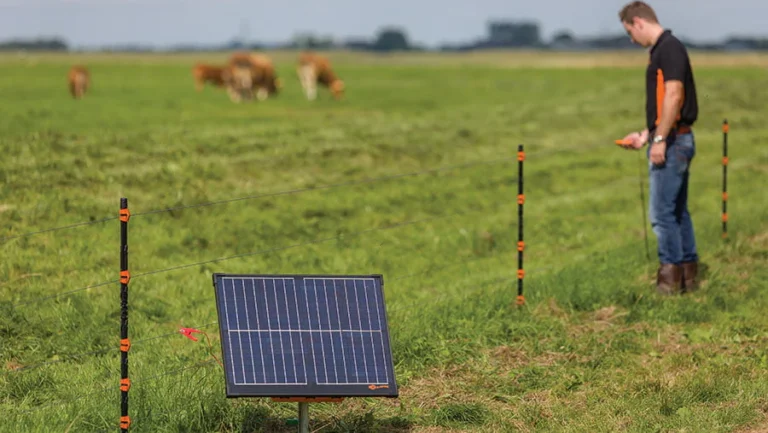
Scenario A: Large-Scale Livestock Management
In an 8,000-acre cattle ranch, the priority is not “intruder detection” but “containment and health.”
-
The Hardware Choice: Monitored pulse electric fencing with LoRaWAN gateways.
-
Constraint: The sheer distance means that if a wire is down, the rancher needs to know the exact GPS coordinate of the fault.
-
Failure Mode: A lightning strike can fry the ungrounded energizer, leaving the perimeter “dumb” until a manual reset occurs.
Scenario B: Critical Infrastructure (Power Substation)
Here, the goal is 100% detection of human intrusion.
-
The Hardware Choice: Acoustic fiber optic sensors attached to a high-security mesh fence.
-
Decision Point: Should the fiber be buried or fence-mounted? Fence-mounting detects climbing; burying detects tunneling.
-
Second-Order Effect: High-sensitivity settings might trigger during a thunderstorm, leading to “alarm desensitization” among security personnel.
Scenario C: High-End Residential Perimeter
Aesthetics and “invisible” security are the drivers.
-
The Hardware Choice: Hidden tension sensors within the fence posts combined with microwave barriers for the driveway.
-
Constraint: Pets. The hardware must be “pet-immune,” meaning the logic must ignore weights under 50 lbs.
-
Failure Mode: Dense landscaping growth can block microwave sensors, creating “blind spots” that the owner isn’t aware of until an incident occurs.
Planning, Cost, and Resource Dynamics
The financial reality of smart fencing extends far beyond the “sticker price” of the sensors. A significant portion of the total cost of ownership (TCO) is found in the “soft” costs of installation and the “long-tail” costs of maintenance.
When you compare smart fencing hardware, consider the following cost tiers:
-
Direct Costs: The sensors, energizers, cabling, and mounting hardware.
-
Infrastructure Costs: Trenching for power lines, installing solar arrays, and building out the network backhaul (e.g., mounting a 40ft antenna for LoRaWAN).
-
Opportunity Costs: The time spent by staff responding to false alarms or managing the software interface.
Estimated Investment Ranges (Per 500 Meters)
| Expense Category | Entry-Level IoT Electric | Mid-Range Tension | Professional Fiber Optic |
| Hardware | $1,500 – $3,000 | $4,000 – $7,000 | $12,000 – $25,000 |
| Installation | $2,000 – $5,000 | $5,000 – $10,000 | $15,000 – $30,000 |
| Annual Maint. | $500 (Vegetation) | $300 (Calibration) | $1,000 (Software/Inspection) |
| Lifespan | 7–10 Years | 12–15 Years | 20+ Years |
Note: These ranges are estimates and vary wildly based on terrain, soil density (for grounding), and local labor rates.
The Risk Landscape: Failure Modes and Compounding Issues
A smart fence is a complex system, and complex systems fail in complex ways. The most dangerous failures are not “hard” failures (where the system stops working entirely) but “silent” failures (where the system appears to be working but is no longer detecting).
-
Environmental Degradation: Salt spray in coastal areas can corrode sensors within 24 months if they aren’t rated for marine environments.
-
Logic “Spoofing”: A sophisticated intruder might apply a bypass wire to an electric fence, maintaining the circuit’s continuity while they cut a hole in the physical mesh.
-
Network Congestion: If a system relies on a local Wi-Fi or zigbee mesh, an increase in nearby interference (or even thick foliage) can cause packets to drop, delaying alarm notifications by critical minutes.
-
Cyber Vulnerability: As gateways become smarter, they become targets for hacking. An unsecured IoT gateway could allow an attacker to “mute” the fence remotely.
-
Compounding Risk: A power outage during a heavy storm. The storm increases the chance of a tree falling on the fence, while the power outage might have disabled the primary sensors, forcing the system to rely on limited-capacity backup batteries.
Governance, Maintenance, and Long-Term Adaptation
Owning a smart fence is more akin to owning a fleet of vehicles than a piece of static real estate. It requires a governance structure to ensure it remains operational.
The Layered Maintenance Checklist
-
Weekly (Automated): Run a “heartbeat” check on all nodes to ensure they are reporting to the gateway.
-
Monthly (Physical): Inspect the physical wire tension. Fluctuations in temperature can slacken wires, leading to inaccurate sensor readings.
-
Quarterly (Technical): Test the grounding system. In many regions, soil moisture levels change seasonally, which affects the efficiency of electric fence pulses.
-
Annually (Strategic): Review the logs. Are there certain zones that trigger more often? Is this due to wildlife patterns or hardware degradation?
Long-term adaptation involves “tuning” the software logic. As the environment changes—new buildings nearby, different vegetation, or changing weather patterns—the thresholds for what constitutes an “alarm” must be adjusted. This is where the value of high-quality hardware becomes apparent; cheaper systems often have “fixed” logic that cannot be updated to account for environmental drift.
Measurement, Tracking, and Evaluation
How do you know if your investment to compare smart fencing hardware was successful? You must move beyond the binary of “did we get robbed?” and look at leading indicators.
Quantitative Indicators
-
Uptime Percentage: The ratio of time the system was fully operational versus in a “fault” or “offline” state.
-
Detection Accuracy: Of the triggered alarms, how many were “verified” (human/animal) vs. “unverified” (wind/ghost)?
-
Latency: The time between a physical breach and the notification appearing on the responder’s device.
Qualitative Signals
-
Staff Trust: If security personnel begin to ignore the fence because of frequent false alarms, the system has failed regardless of its technical specs.
-
Deterrence Factor: Observing (via cameras) individuals approaching the fence and then turning away because they recognize the “smart” components.
Documentation Examples
-
Fault Logs: A timestamped record of every drop in voltage or tension.
-
Calibration Records: Documentation of the sensitivity settings for each zone.
-
Incident Post-Mortems: A detailed analysis of any successful breach or “near miss.”
Common Misconceptions and Oversimplifications
-
Myth 1: “Smart fences are self-maintaining.” * Correction: They actually require more specialized maintenance than traditional fences, as you are managing both physical and digital assets.
-
Myth 2: “Wireless sensors are always better.” * Correction: Wired sensors are generally more reliable and harder to jam, though they are more expensive to install.
-
Myth 3: “Electric fences are dangerous to humans.” * Correction: Modern smart energizers use “safe” pulses that are unpleasant but not lethal, complying with international safety standards (IEC).
-
Myth 4: “I can just use cameras instead.” * Correction: Cameras are reactive and can be blocked by weather or darkness. A fence sensor is a physical “tripwire” that works 24/7 regardless of visibility.
-
Myth 5: “Solar power is a ‘set it and forget it’ solution.” * Correction: Solar panels require regular cleaning and battery replacements every 3–5 years to maintain peak performance.
-
Myth 6: “All smart fences integrate with all security software.” * Correction: Proprietary hardware often creates “walled gardens,” making it difficult to integrate a specific fence brand with your existing CCTV or VMS software.
Synthesis: The Future of Perimeter Intelligence
As we compare smart fencing hardware, it becomes clear that the value of these systems lies not in the wires themselves, but in the quality of the data they produce. A high-quality smart fence transforms a boundary from a liability that must be patrolled into an asset that provides continuous, actionable intelligence.
The future of this field is likely moving toward “edge-AI” sensors—hardware that doesn’t just send a raw signal to a computer, but actually “thinks” at the fence line. These sensors will be able to distinguish between a deer jumping a fence and a person cutting it before the data even reaches the cloud.
For the property owner, the goal is resilience. A resilient system is one where the hardware is over-specified for the environment, the network is redundant, and the human operators are trained to interpret the system’s output. In the long run, the most expensive smart fence is the one that is poorly matched to its environment, as the costs of false alarms and missed detections far outweigh any initial savings on hardware procurement.